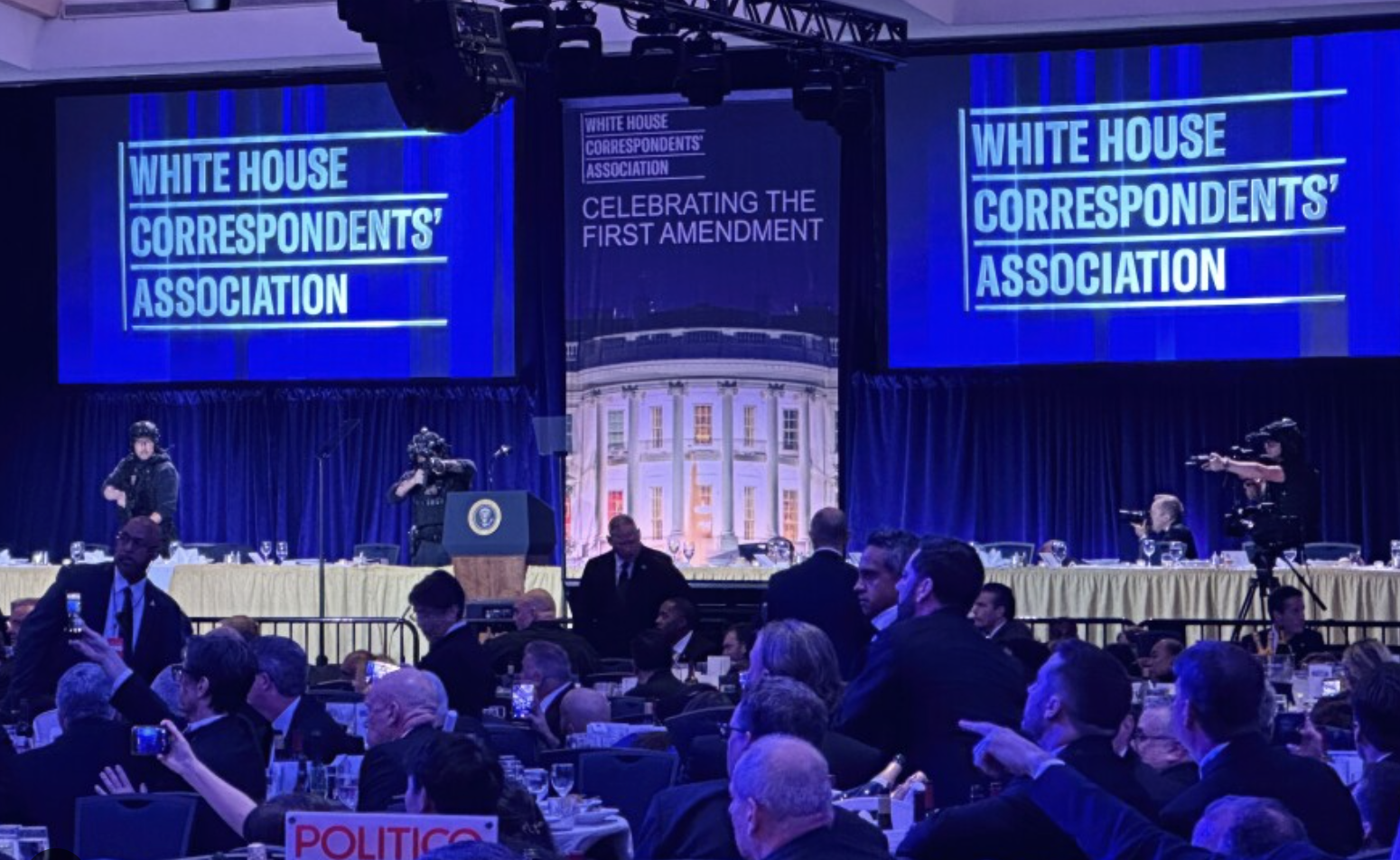
Saturday April 25, 2026, at the White House Correspondents’ Association dinner, an armed man rushed the magnetometer at the Washington Hilton with a long gun in plain view. A U.S. Secret Service officer wearing a ballistic vest was shot in the chest. The officer drew his weapon and returned fire. The suspect went down at the top of the staircase leading to the ballroom. He never reached the room.
The protective layer worked. By inches.
The room did not work the same way. According to NPR reporters in attendance, the ballroom fell into “eerie silence” and “a lot of confusion.” Trump, Vance, the First Lady, and Cabinet members were rushed out by Secret Service. Members of congressional leadership, who travel with Capitol Police protective details, were evacuated. Rank-and-file lawmakers were left locked down inside the ballroom with no clear plan, according to one House GOP attendee who described being “surprised and unsettled” by the gap. Some guests ran for exits. Others lingered. Some hid under tables for four to five minutes. A White House Deputy Chief of Staff tried to start a “U-S-A!” chant during the evacuation.
The accused, Cole Tomas Allen, 31, was not someone who slipped through the perimeter on event day. He had checked in to the Washington Hilton on April 24, the day before the dinner. He had booked the room on April 6. He came down from a 10th-floor room with a shotgun, a handgun, and knives, and he reached the screening checkpoint before anyone stopped him.
If you are an event director, marketing leader, or chief of staff responsible for a high-profile corporate event in 2026, this guide is for you. It explains what the WHCA incident actually teaches the rest of us, the public threat-assessment doctrine your team should be reading directly, and the operational disciplines that separate real security plans from security theater.
It is written from 20+ years of work on events for the Library of Congress, the Department of Defense, the U.S. Department of Energy, Presidential campaign events, and Fortune 500 C-Suite meetings hosted alongside the United States Secret Service, Capitol Police, Diplomatic Security, the White House Advance team, the State Department, and federal, state, and local law enforcement.
Bottom line. A reactive plan is the illusion of safety. A proactive plan is the real thing. WHCA is the cleanest illustration in years of why the difference matters. Here is how to fix yours before your next event.
Reactive vs Proactive: The Two Postures of Event Security
A reactive plan is designed to respond after a breach. Uniformed officers in the lobby, magnetometers and bag checks at the door, marked law enforcement vehicles parked out front. The team is ready to move when something happens. Most clients look at this and feel safe. It looks like security.
A proactive plan is designed to make the breach impossible. The bad actor never gets close enough to require a reactive response. The plan anticipates the threat vectors, closes them off in advance, and architects layers between the public street and the principal-occupied space such that an incident at one layer cannot propagate to the next.
Both plans have armed officers. Both plans have screening. The difference is intent and architecture. A reactive plan is built around response time. A proactive plan is built around prevention.
WHCA is a useful test case for the distinction. The screening layer was reactive in the best sense of the word. It held under live fire. But the outer layers, where a proactive plan stops a bad actor before they ever reach a magnetometer, did not. Allen booked a room three weeks in advance, traveled cross-country by train, checked in 24 hours before doors, and came down from his floor with weapons visible. None of that should have produced a person at a checkpoint with a long gun, and a proactive posture is what would have changed it. The Washington Post reported that the dinner was not given top security status that would have unlocked the full weight of federal resources, even though it concentrated the President, Vice President, FBI Director, multiple Cabinet secretaries, and roughly 2,600 attendees in one ballroom. Former FBI Deputy Director Andrew McCabe told NBC News the security posture should have been “almost on the level of a national security event.”
The federal protective elements are excellent at the proactive posture for their assigned principals. Where commercial events fall down is the rest of the room. The Secret Service has a duty to its protectees. Capitol Police, Diplomatic Security, and the protective apparatus around them operate the same way. By that measure, WHCA worked. But the duty of care to the thousand-plus other people in the room is yours, not theirs. After WHCA, after the UnitedHealthcare CEO shooting in late 2024, after a string of incidents at high-profile gatherings, that gap is now a board-level liability.
The fix is not exotic. It is five disciplines.
The Five Disciplines That Separate a Real Plan From Theater
If you do nothing else after reading this, do these five things before your next event.
- Build a layered architecture. Defense in depth. Concentric protective zones from the public street to the principal-occupied space, with controlled access, controlled movement, and controlled sightlines at every layer.
- Lock down the operational elements. Hold rooms, hard rooms, SCIFs where required, line-of-sight planning, secure movements, and at least three layers of alternates for every primary action.
- Write your pre-decisional triggers. What happens at credible breach, suspicious package, threat to principal, active threat indicator. Each trigger has one named decision authority and a pre-rehearsed response. Onsite is execution, not deliberation.
- Extend your threat window to 24-48 hours, longer when the principal warrants it. Especially in hotels. The day-of is too late. Pre-event sweeps, lockdown of the event floor, full chain-of-custody for every delivery and piece of equipment, overnight security presence, and vendor vetting tied to specific zones and time windows.
- Engineer communications as safety infrastructure. Hardened network with redundant backhaul, separate operational network, pre-recorded PA announcements, pre-designed screen slides, pre-loaded push notifications, designated authority chain. The WHCA gap was here.
The rest of this guide is each one, expanded.
Discipline 1: Build a Layered Architecture
The foundational concept of serious event security is defense in depth. The term originates in military doctrine and is formalized across the Department of Defense, cybersecurity practice, and Crime Prevention Through Environmental Design (CPTED). The principle is simple. No single barrier is sufficient. Security is the cumulative effect of multiple, overlapping, independent layers, each designed so that failure at one does not propagate to the next.
Before your team hires a security vendor, evaluates the one you already have, or signs off on a plan someone else built, you should be reading the public doctrine directly. We do, and we expect the security partners we bring onto our events to do the same. The most useful sources, with direct links:
- DHS CISA Securing Public Gatherings is the federal hub for soft-target and mass-gatherings security. The accompanying Mass Gatherings: Security Awareness for Soft Targets and Crowded Places and Security of Soft Targets and Crowded Places — Resource Guide are the most accessible federal starting points.
- U.S. Secret Service National Threat Assessment Center publishes the Mass Attacks in Public Spaces report series. The most recent five-year synthesis, Mass Attacks in Public Spaces: 2016–2020, analyzes 173 targeted attacks and identifies the pre-attack behavioral indicators that consistently appeared in the months and weeks before incidents. It is free, current, and the most applied research available on how attacks at gatherings actually unfold.
- The FBI publishes targeted-violence prevention guidance and operates InfraGard, a public-private threat-information sharing partnership any qualifying organization can join.
- The Event Safety Alliance Event Safety Guide is the closest thing to a unified standard for live-event safety planning. The full guide is available as a free PDF, along with ANSI consensus standards on event security, crowd management, weather, and communications. Decibel Events is a member.
- ASIS International publishes the professional standards behind CPTED and physical asset protection.
What this looks like at an event. Outer control of approach, with vehicle and pedestrian standoff and credentialed pre-check. Controlled funnels with no free movement toward checkpoints. Effective screening with sufficient throughput so the line never backs up onto the public sidewalk and becomes the new soft target. A buffer zone between screening and the principal-occupied space. An interior designed for response, where aisle widths, exit pathways, principal positioning, and media isolation are security decisions before they are hospitality decisions.
These principles are not proprietary. They are public. The job of a serious production partner is to apply them rigorously and refuse to compromise them for stage sightlines or guest experience.
Discipline 2: Lock Down the Operational Elements
The architecture is the spatial layer. Underneath it, a serious plan includes operational elements most clients have never heard of.
Hold rooms. Where the principal waits before going on. Secure, monitored, single point of access, tied to the secure movement plan.
Hard rooms. Where the principal goes if something happens. Pre-designated, lockable, hardened. With comms and a defended access route. Not a back office. Not a green room. A purpose-designated hard room.
SCIFs. When the event involves classified discussion or cleared government principals, a Sensitive Compartmented Information Facility on site or adjacent. Not every event needs one. The events that do cannot proceed without one.
Line-of-sight planning. What can be seen from where, and what cannot. Not only where snipers would set up if they were planning this (windows, balconies, mezzanines, adjacent buildings) but line-of-sight to the crowd and attendees for all of the principal movements. Every elevated position within the visual range of the principal is a planning input.
Secure movements. How the principal arrives, moves from LZ or motorcade drop to hold room, to stage, to exit. Every movement rehearsed. Every alternate route mapped. Every choke point staffed.
Alternate plans. What happens if the primary entrance is compromised, if the motorcade is delayed, if the venue itself becomes unsafe and we evacuate to a secondary location. A real plan has at least three layers of alternates.
These elements do not show up on the agenda you send the client. They live in the security operations document, which sits separately from the run of show, and they are the difference between a binder of intentions and an executable plan.

Discipline 3: Write Your Pre-Decisional Triggers
The closest similar pre-decision trigger protocol we have to this is weather based. Decibel runs a High Wind Action Plan on every outdoor or partially exposed event. The plan specifies, before doors open, the exact wind speed thresholds at which staging is reinforced, at which guest movements are halted, when crew movements are halted backstage, and at which the program shuts down entirely. The triggers are written. The decision authorities are named. The actions are pre-rehearsed.
Onsite, when the wind hits the threshold, nobody is debating. Nobody is asking the client. The action happens.
That same framework needs to apply to security decisions, and it almost never does.
A serious plan defines pre-decisional triggers for every credible scenario:
- When there is a credible perimeter breach, posture changes to X. The named lead security ops authority calls it. Full stop.
- When a suspicious package is identified, the package is isolated, the protocol runs, EOD is called, program continuity is decided by the named authority. No client phone tag.
- When there is a credible threat to a principal, the principal goes to the hard room via the pre-walked route. Detail leadership calls it. The producer is notified.
- When an active threat indicator is inside the venue, the lockdown protocol fires. The pre-recorded PA announcement plays. The pre-designed screen slide flips. The doors that should lock, lock.
- When an active threat indicator is identified outside the venue, the shelter-in-place protocol fires. Different announcement, different slide, different action.
Each trigger has a single named authority. Each action is pre-walked, pre-rehearsed, and documented. Onsite is not the time to debate posture. Onsite is the time to execute the decision the leadership team already made in the planning phase.
WHCA is what happens without this discipline at the attendee layer. Different people in the same room made different decisions in the same moment because no decision had been pre-made for them. If your client cannot answer the question “what happens at threshold X” with a one-sentence answer in advance, your plan is not a plan.
Discipline 4: Extend Your Threat Window 24-48 Hours, Longer When the Principal Warrants It
The day of the event is not the security window. The actual threat window starts at least 24 to 48 hours earlier, sometimes longer, and almost no corporate event plan reflects that.
WHCA is the proof point. According to the Department of Justice charging affidavit, Allen booked his Washington Hilton room on April 6, 2026, for three nights starting April 24. He traveled cross-country by train, arriving in DC the afternoon of April 24. He was in the building, in a 10th-floor room, more than 24 hours before he came downstairs with weapons. His name was on a hotel reservation list at the venue hosting one of the highest-profile political events of the year, and the dinner did not receive the security status that would have unlocked the federal resources to do anything about that.
This is the structural risk in hotels. Hotel ballrooms and event floors are connected to a building that is fundamentally open. Adjacent rooms are bookable by anyone with a credit card. Service corridors are accessible to housekeeping, banquet staff, room service, engineering, and any of their unbadged contractors. HVAC, water, freight elevator, loading dock, and back-of-house pathways feed directly into the event space. A bad actor with even modest planning can pre-position an item, or themselves, in any of these areas hours or days before doors open.
A serious 24- to 48-hour threat assessment includes:
- Pre-event canine sweeps of the event space, adjacent rooms, service corridors, and back-of-house pathways, completed before secure setup and again before doors
- Technical surveillance countermeasures (TSCM) sweeps for events with sensitive content, executive principals, or classified material
- Lockdown of the event floor and adjacent rooms for the pre-event window, with controlled access by named, badged personnel only
- Loading dock and freight access controlled with a manifest, sign-in/sign-out, badged escorts for drivers and crews, and inspection at entry. Every piece of equipment accounted for from sender to staging area
- Air handling, water, and food chain control, including kitchen and catering staging
- Adjacent room and floor blocking when budget and venue cooperation allow, including the floors above and below the event space for high-principal events
- Cross-reference of hotel guest lists for the event window against threat watchlists where law enforcement coordination supports it
- Vendor and crew vetting tied to specific zones and time windows
- Surveillance detection routes walked by the security team during the window
- Overnight security presence inside the controlled footprint
For events where the principal warrants it, this window extends to 72 hours or longer. The point is that the day-of plan is not the plan. If the only people in your venue at 3 a.m. the night before doors are housekeeping and a single hotel guard, your threat window is wide open. That is not a hypothetical anymore. That is the WHCA timeline.
Discipline 5: Engineer Communications as Safety Infrastructure
This is the line item that gets cut first and matters most. It is also the layer where WHCA failed.
WiFi and Network Are Safety Systems, Not Hospitality Line Items
Event WiFi is expensive. Properly engineered event communications infrastructure is more expensive. Almost every client we work with starts the budget conversation by asking whether they can get away with house WiFi and rely on cellular for the rest. The honest answer is: not for a serious event in 2026.
In a real incident, your security ops team needs encrypted, low-latency communications between the perimeter, the screening zone, the buffer, the principal detail, and the production booth. If those comms ride on the same shared WiFi that two thousand attendees are using to check social media, your security architecture has a single point of failure that anyone can saturate by accident, and that a bad actor can saturate on purpose.
Cellular is not a backup. In high concurrent device counts, cellular saturates. In basement ballrooms, cellular does not exist. In a credible threat environment, cellular can be deliberately degraded.
Push notifications, SMS to attendees, event app updates, digital signage that flips to the lockdown slide on cue. Every one of these is network-dependent. Every one fails if your network is fragile.
What a serious comms infrastructure looks like:
- A dedicated event WiFi network with sufficient bandwidth and access point density for actual concurrent load, separated by VLAN from operational traffic
- A separate, hardened operational network for security, production, and registration only
- Carrier-grade redundant backhaul, ideally split across two carriers
- Cellular boosters or distributed antenna systems where coverage is poor
- Battery and generator backup for network gear
- A pre-tested public address system with battery backup and pre-recorded announcement files for the most likely scenarios
- Digital signage and stage screens cabled to a controller that can flip to pre-designed lockdown, shelter, and evacuation slides on a single keystroke
If your event communications strategy depends on the venue’s house WiFi and a hope that cellular will hold, your security plan is fragile by design.
The Attendee Communications Plan WHCA Did Not Have
A serious attendee comms plan includes a designated event-facing voice with the authority to address the room, pre-cleared by security ops and trained on the scripts. Pre-written scripts for the most likely scenarios: lockdown, shelter, evacuation, medical, threat external, threat internal. Pre-recorded PA announcements loaded and ready, because in an actual incident a calm pre-recorded voice is faster, clearer, and less stress-affected than a live read. Pre-designed screen slides for stage, side, and digital signage with single-keystroke flip. Pre-loaded SMS and push notifications ready to fire from a designated authority’s device, with templates approved in advance and triggers tied to the same pre-decisional thresholds security ops is using.
It includes redundant channels, because in a real incident one of them will fail. PA, house lighting changes, digital signage, SMS, event app push, designated staff with handheld signage. It includes clear evacuation paths and muster points briefed at the top of the event, because five seconds of “in the unlikely event of an emergency, our exits are here, here, and here, our muster point is the corner of X and Y” is the cheapest insurance you will buy all year. It includes a designated authority chain for who decides to evacuate, who sends the message, who tells AV to cut the program, all agreed in advance. And it includes a post-incident comms plan for what gets said to attendees, the press, and the public after.
The WHCA ballroom on April 25 seemed to have none of this. Some attendees ran. Some hid. Some lingered. Some continued eating. Some took the wine. A senior White House aide tried to start a “U-S-A!” chant. Lawmakers without protective details remained with no instructions. That is not a security failure in the principal-protection sense. It is a crowd-care failure in the event-organizer sense, and it is the layer most events miss.
The Agency Layer: Why Integration Is the Job
A proactive plan is not built by one team. On a single high-stakes event we may be working with the United States Secret Service, Capitol Police, Diplomatic Security Service, the White House Advance team, the State Department, local police and sheriff’s departments, third-party security vendors, venue security and engineering, and on-site medical and EMS.
Each has its own planning cycle, its own protocols, and its own decision authority. The job of the event production partner is to integrate all of them into a single coherent plan, work with the contracted security vendor for walk-throughs together, deconflict the coverage, and make sure every layer is talking to every other layer. That is the work. It is not a service line you can buy off the shelf, and it is not something you should expect a venue’s house operations team to handle. It is what we do, and across 20+ years it has been the thread that holds our events together.
How Decibel Approaches Event Security: Introducing Decibel Secure
We treat security as a workstream, not a service line. From the day a project starts, the security architecture is being built in parallel with the creative, the production, and the program. Site visits include a security walk-through. The run of show is reviewed against the security ops document. Every phase, from initial discovery through post-production, has a security check-in built in. The five disciplines above are how we approach every event — corporate, association, government, conference, and activation alike.
Some events require more than that.
For engagements where the threat model is fundamentally different, defense and defense-tech, federal and DoD work, financial services M&A and MNPI (material non-public information) gatherings, pharma R&D summits, and high-profile individuals, we operate a separate, paid practice called Decibel Secure. Secure is not the disciplines discussed above turned up louder. It is a different production model, scoped under mutual NDA from the first call, in which the leak surface is engineered out of the work itself.
What changes under Decibel Secure: crew are NDA-bound and cleared where the engagement requires it, sourced as a small senior team rather than rotating freelancers; device discipline is enforced at intake through Faraday pouches, credentialed lockers, or no-device zones; the network the event runs on is one we deploy, with enterprise-grade firewalls and segmented VLANs, isolated from the venue’s public infrastructure that has been a documented target of state-sponsored campaigns for more than a decade; information protocol governs what gets captured, by whom, and where it goes after; executive protection coordination integrates with the client’s EP team from advance through wrap; and federal contracting paperwork is already on file under an existing GSA Schedule.
One room. One crew. Zero posts.
Decibel Secure engagements begin with a confidential consultation under mutual NDA. No marketing drip, no unsolicited follow-up. If your event sits in that profile, reach David Sonntag directly at david@decibelevents.com.
“David is one of the most top notch professionals I have ever worked with. His ability to calmly manage, navigate and create an event is flawless.” — Alice Lutz, CEO, Triangle Family Services
That calm under pressure is not personality. It is the result of a plan built for the day everything goes wrong.
Don’t Wait for an Incident to Rebuild Your Plan
The events that handle this correctly do the work before the headlines force them to. The events that get caught off guard are the ones that assumed visible security was the same as effective security. After WHCA, the line between those two postures is sharper than it has ever been.
If you are responsible for a corporate, government, or association event and you are not certain your current plan is proactive, reach out to the Decibel team. The five disciplines above are the standard we bring to every engagement.
If your event fits the Decibel Secure profile (defense, federal, financial M&A, pharma R&D, or principal-level) that is a different conversation, held under mutual NDA from the first call. david@decibelevents.com is the direct line.
20+ years of perspective and the agency relationships to back it up.
Yeah, we can handle that.®
Frequently Asked Questions
Did security fail at the White House Correspondents' Association dinner?
Partially. The screening layer worked. The accused, Cole Tomas Allen, reached the magnetometer at the screening checkpoint with a long gun visible. A Secret Service officer was shot in the chest, his ballistic vest stopped the round, and the officer returned fire and neutralized the suspect before he reached the ballroom. By the measure the screening was designed to meet , keeping the principals safe, it succeeded.
The broader posture had documented gaps. The Washington Post reported the dinner was not given top security status, which would have unlocked additional federal resources, despite the concentration of senior officials in attendance. The biggest gap was attendee communication. Members of congressional leadership with their own protective details were evacuated; rank-and-file lawmakers were locked down inside the ballroom without a clear plan, a gap the event organizer is responsible for.
The scroll generation refers to attendees who were raised consuming content through social media feeds, short-form video, and algorithmic platforms. Their attention patterns are fundamentally different from previous generations. They expect rapid pacing, constant stimulation, and zero dead time. For corporate events, this means traditional formats built around long, unscripted sessions are becoming structurally incompatible with how your audience processes information. This is not a preference they toggle off at a conference. It is how their brains were trained to work, and it changes the production requirements for any event that wants to hold their attention.
What is the difference between reactive and proactive event security?
A reactive plan is designed to respond after a breach. A proactive plan is designed to make the breach impossible by controlling space, distance, flow, and access at every layer between the public and the principal. Both plans have armed officers and screening. The difference is whether the architecture stops a bad actor before they reach the protected space, or only responds once they have. The gold standard is proactive.
Why is attendee communication considered the biggest gap at most events?
Because the federal protective agencies are not responsible for the crowd. They are responsible for their assigned principals. If the event organizer has not built a separate attendee communications plan, with pre-recorded PA announcements, pre-designed screen slides, pre-loaded push notifications, redundant channels, a designated authority chain, and rehearsed muster points, then attendees are on their own in an incident. NPR reporters in the WHCA ballroom described “eerie silence” and “a lot of confusion” as the gap played out in real time.
Why should event WiFi and communications be treated as safety infrastructure?
Because every modern incident response action is network-dependent. Push notifications, SMS, event app updates, encrypted security comms, and digital signage all require a functioning network to fire. Cellular saturates in high-density venues and can be deliberately degraded. House WiFi is shared with attendees. Serious events budget for a dedicated event network with redundant backhaul, a separate hardened operational network, battery and generator backup, and pre-tested PA with pre-recorded announcement files.
What are pre-decisional triggers in event security planning?
Pre-decisional triggers are written thresholds that automatically initiate defined security actions without onsite debate. The model is the High Wind Action Plan most production teams use for outdoor events: specific thresholds, named decision authorities, pre-rehearsed responses. Applied to security, this means defining in advance what happens at a credible breach, a suspicious package, a credible threat to principal, an active threat indicator inside or outside the venue. Onsite is execution, not deliberation.
Why does threat assessment need to begin 24 to 48 hours before doors open?
Because the threat window does not start at doors. The accused at WHCA had been a paying guest in the venue hotel since the day before the event, with the room booked three weeks in advance. In hotels especially, adjacent rooms are bookable, service corridors are accessible to dozens of unbadged staff, and back-of-house pathways feed directly into the event space. A serious 24- to 48-hour assessment includes pre-event canine sweeps, lockdown of the event floor, chain-of-custody for freight, adjacent room and floor blocking, vendor and crew vetting, and an overnight security presence inside the controlled footprint. For high-principal events the window extends further.
What public resources should our team be reading on event security?
Start with CISA Securing Public Gatherings and the Soft Targets and Crowded Places Resource Guide. Read the U.S. Secret Service National Threat Assessment Center Mass Attacks in Public Spaces: 2016–2020 report for the behavioral pre-attack indicators that consistently appear before incidents. The Event Safety Alliance Event Safety Guide is the closest thing the live-event industry has to a unified standard. InfraGard and ASIS International round out the practitioner library.

About the Author
By David Sonntag, CEO & Executive Producer, Decibel Events
David Sonntag is the CEO and Executive Producer of Decibel Events, a full-service event production, design, and management company headquartered in Washington, DC. He has been producing live events since 2003, including on the National Mall and with the National Park Service. For more than 14 years, David has served as the event producer for the Library of Congress National Book Festival.
He is also a former Vice President at Fleishman-Hillard, where he gained extensive experience in message development and delivery.
David’s expertise spans technical production, event design, event management, and marketing communications. His events have earned seven Silver Anvil Awards, eleven Telly Awards, two PR Week Awards, and many other industry honors. The Triangle Business Journal also selected David for the 40 Under 40 Leadership Awards in 2017.
Under David’s leadership, Decibel Events has been continuously listed on the Washington Business Journal’s Largest Meeting and Event Planners ranking every year since 2019. To learn more or discuss your next event, contact David at David@DecibelEvents.com or 703.953.4493.